To date the Pharma industry has not leveraged the wealth healthcare data volumes to deliver truly personalized care for patients.
On Monday 23rd of August the Applied Machine Learning Days (AMLD) hosts the AI & Pharma track, consisting of 4 sessions:
(i) methodological innovations in data science, ML and AI;
(ii) applications / use cases;
(iii) data sharing, ethics and privacy;
(iv) panel discussion on the adoption of AI in Pharma – solving the data Conundrum.
This track is co-organised by the Roche, Novartis and C4DT.
For more information click below.
To promote research and education in cyber-defence, EPFL and the Cyber-Defence Campus have jointly launched the “CYD Fellowships – A Talent Program for Cyber-Defence Research.” The fourth call for proposals is now open with a rolling call for Master Thesis Fellowship applications, and with a deadline of 16 August 2021 for Doctoral and Distinguished Postdoctoral Fellowship applications. CYD fellows are hosted by a higher education institution in Switzerland and conduct their research at the CYD Campus located on the premises of EPFL and ETHZ and in its office in Thun. For more details visit the program’s dedicated website by clicking the link below or join the online Applicant Workshop on 5 August 2021 from 10.00 to 10.45 CEST (for more information please contact research@epfl.ch).
If weakening encryption through legislation or judicial orders is not the right solution, are there other ways to reconcile privacy, security and public safety? How can policymakers ensure a coherent approach on apparently divergent policy objectives? What can the EU do to promote encryption? Can government agencies develop new investigative techniques without undermining encryption?
Trust in Innovation is a 100% digital event that will take place on June 16th , 2021. It targets SMEs wanting to understand and adopt new technologies such as Blockchain, Artificial Intelligence and Quantum Computing. It promises no sales speech but pedagogy and ROI. The key themes treated during the event are traceability, compliance, healthcare and tokenisation.
For more information click below.
Today, it’s often more cost-effective to host services in the cloud instead of in its own premises. But how protected is our sensitive data in the cloud? We readily encrypt data in storage and protect it while in transit. But what about when data is “in use”? It is a legitimate concern in increasingly cloud-dominated infrastructures. Moreover, how to make sense of the different laws governing the sensitive data?
During this week we will explore how privacy-enhancing computation technologies complement a zero-trust strategy by addressing the vulnerability of data in use in the cloud. We will also discuss the legal framework which is required to balance economical interest of companies with the individual’s data privacy concerns.
For more information click below
There is much debate about the use of digital immunity passports as a response to the COVID-19 pandemic. Such digital tools to certify immunity could help spur economic recovery, but raise ethical and privacy concerns. How to build trust in such a solution? What elements make them interoperable among countries? How is people’s data related to their immunity status governed?
A panel of prominent specialists will discuss these and other questions from 4 different angles – ethical, business, political/governance and scientific – during a two-hour moderated discussion.
For more information click below.
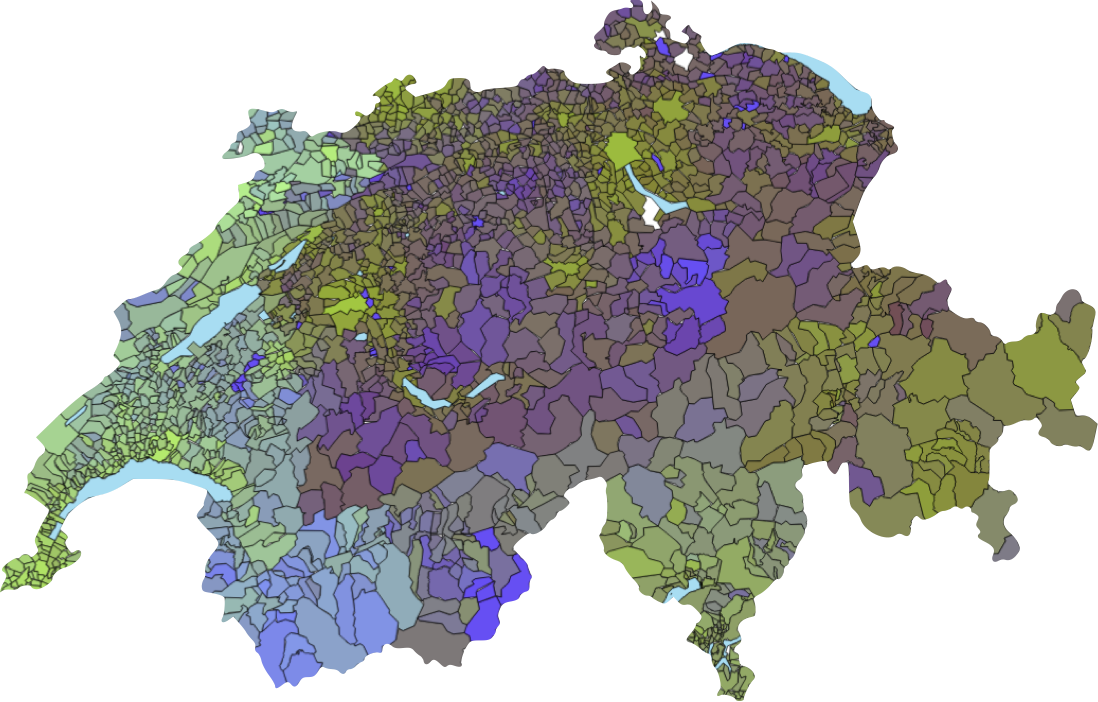
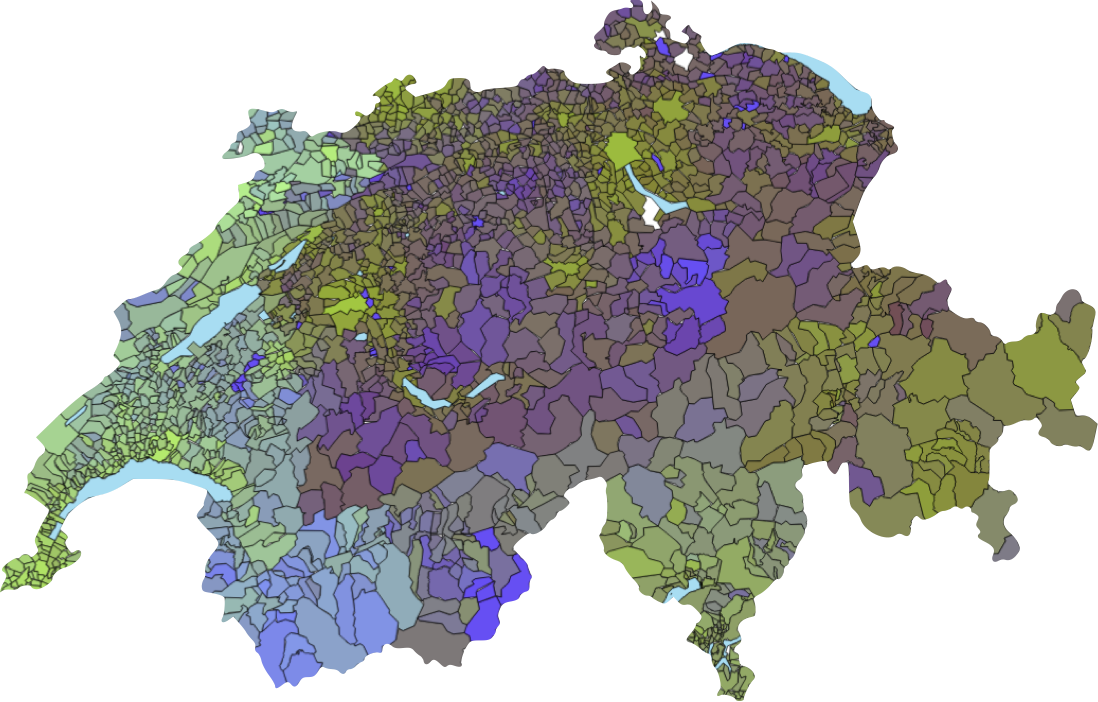
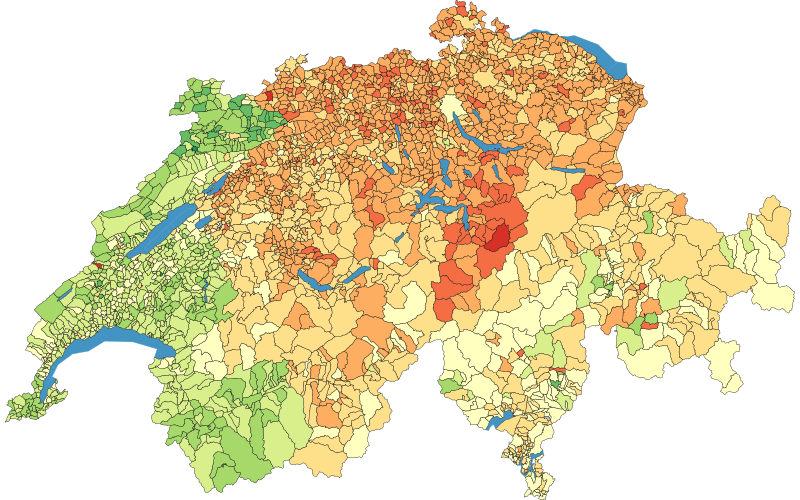
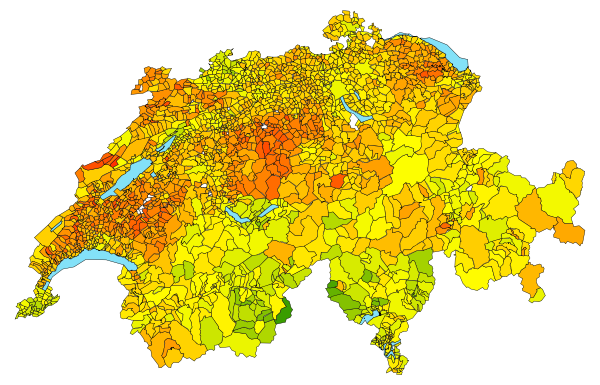
On the 7th of March, the Swiss population voted on a ban for full face coverings, the e-ID Act, and an economic partnership agreement with Indonesia. As with all Swiss referendums since 2019, the EPFL election prediction tool Predikon generated real-time predictions for the vote outcomes.

Digital activities represent around 4-5% of CO2 emissions, estimate several studies. And cryptocurrencies, like Bitcoin, are amongst the most energy consuming activities: far ahead of streaming and email exchanges. The podcast “Le Point J” tries to understand why.
In communication systems, there are many tasks, like modulation recognition, for which Deep Neural Networks (DNNs) have obtained promising performance. However, these models have been shown to be susceptible to adversarial perturbations, namely imperceptible additive noise crafted to induce misclassification. This raises questions about the security but also the general trust in model predictions. In this project, we propose to use adversarial training, which consists of fine-tuning the model with adversarial perturbations, to increase the robustness of automatic modulation recognition (AMC) models. We show that current state-of-the-art models benefit from adversarial training, which mitigates the robustness issues for some families of modulations. We use adversarial perturbations to visualize the features learned, and we found that in robust models the signal symbols are shifted towards the nearest classes in constellation space, like maximum likelihood methods. This confirms that robust models not only are more secure, but also more interpretable, building their decisions on signal statistics that are relevant to modulation recognition.
Cyber security information is often extremely sensitive and confidential, it introduces a tradeoff between the benefits of improved threat-response capabilities and the drawbacks of disclosing national-security-related information to foreign agencies or institutions. This results in the retention of valuable information (a.k.a. as the free-rider problem), which considerably limits the efficacy of data sharing. The purpose of this project is to resolve the cybersecurity information-sharing tradeoff by enabling more accurate insights on larger amounts of more relevant collective threat-intelligence data.
This project will have the benefit of enabling institutions to build better models by securely collaborating with valuable sensitive data that is not normally shared. This will expand the range of available intelligence, thus leading to new and better threat analyses and predictions.
Current digital trends and innovation, including artificial intelligence, cybersecurity, data privacy, blockchain and digital trust, are rapidly changing and disrupting the way donors, employees, and beneficiaries interact with each other. Technology can be a powerful tool for philanthropic and non-profit organizations, accelerating their digital transformation through automating and streamlining business processes, using digital platforms, and leveraging data and analytics in new ways that enhance their efficiency and social impact.
This Monday I presented the following article. It discusses blockchains shortcomings. Even if it has been written in 2018, it is still very up-to-date… What follows here is a very opinionated piece. As such it reflects the journey I did in blockchains over the past 6 years. And I’m sure I missed out a lot (…)
Concurrent programming is one the oldest and hardest issues in the Computer Science Book. For years, we have been using locks, big threads sharing the minimum, using optimistic reasoning for “how data will be updated”. And we are still stuck with the same issues of some part of the code “failing” to use the updated (…)
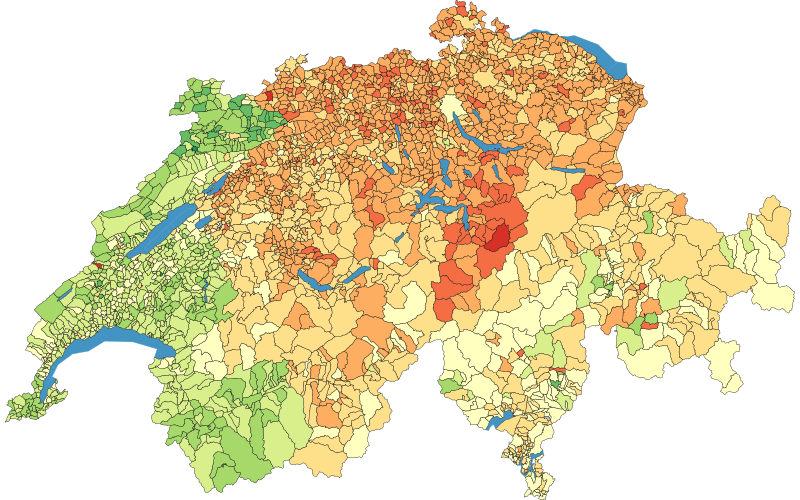
On March 7, the next Swiss referendum vote will be held, with votes on a ban for full face coverings, the e-ID Act, and the economic partnership agreement with Indonesia. As this national vote approaches, the EPFL election prediction tool, Predikon, is rolling out some improvements with new features.
We’ve been looking at the very nice https://gather.town and played around with it. Instead of having a fixed view of all participants, you can walk around and ‘meet’ different persons in gather.town. You can edit the space your liking. It looks very much like a very old-school Zelda: What I liked a lot about it (…)
The management of IT infrastructure is a constantly evolving topic. A very interesting concept that emerged in the last decades is the idea of infrastructure as code: instead of configuring servers in an artisanal fashion, the process is formalized into definition files, which are then automatically “executed”. There are multiple advantages, notably: The files always (…)
Code formatting is the most known instance of bikeshedding: everyone has a different opinion on it and nobody is willing to compromise. Do you remember the hours-long discussions on using tabs versus spaces? Where to add empty lines? Alignment of fields? For some years now, many languages provide their own code formatter, Go has gofmt, (…)

EPFL Professor Matthias Grossglauser has been awarded the grade of Institute of Electrical and Electronics Engineers Fellow, a notable recognition given to less than 0.1% of voting members annually.
Please click below for more info.
On the 7th of March the Swiss population will vote on a law the Federal Council and the Parliament have prepared establishing an identification system recognized by the Confederation: the e-ID. Opportunities that arise through digital identification will not only depend on a country’s implementation but also on the trust which its citizens have in its government and institutions. During the week of the 8th to 12th of March, which follows the referendum, we would like to
– discuss the eID law and compare it to the one already implemented by other countries,
– discuss the population’s trust and willingness to adopt a national eID,
– get the perspective of a Swiss Consumer group and learn about the tech implementation and perspective of a digital ID provider,
– hear researchers’ point of view on the implementation challenges, possible solutions and research trends.
Finally, we will try to identify and frame a challenge / use case on which the eID workgroup can solve with the support of research.
Please note that this is a C4DT community event only.
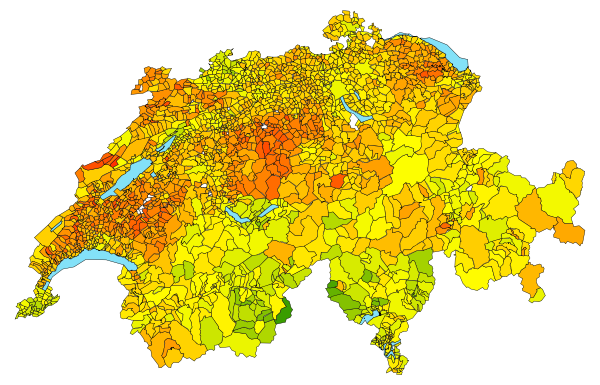
While votes seem to yield increasingly surprising results, such as the election of Donald Trump in 2016 or the Brexit vote in the UK defying pre-vote polls and initial vote counting predictions, Swiss vote results are swiftly being predicted by Predikon. We will follow the evolution of the project until the next vote, which will take place on March 7th. An article every month will enable you to observe the evolution of the project, (almost) live, accompanying Victor Kristof in the improvement of Predikon.
C4DT’s Factory provides a hands-on technical training for C4DT partners on a tool called Calypso. This tool allows to store secrets on a blockchain, and to dynamically update the access control. The hands-on training has been initiated by a request from SICPA. They were looking for a way to store the private keys used in (…)
During this event the 4 associate partners, who joined the C4DT as part of the C4DT start-up program, will present themselves to the C4DT community. For two years Regdata, strong.network, Taurus and Xorlab will complement the already diverse group of partner companies through their start-up perspective and collaborate and share insights on trust-building technologies. Virtually meet them, learn about their activities and ask questions and discuss with your start-up(s) of interest in 4 concurrent break-out sessions.
This is a C4DT community event only.
This article looks into the optimizations of the golang compiler with regard to different usage of structs. It answers the following questions: Does it avoid unnecessary structure copies? Does it inline where necessary? To answer theses questions, I wrote a small example and decompiled it to see how well it behaves. For all the examples, (…)
We are excited to announce the launch of the C4DT start-up program. 4 start-ups have already been selected to join the C4DT community, consisting of 13 partners and 34 EPFL laboratories, to collaborate and share insights on trust-building technologies. For two years Regdata, strong.network, Taurus and Xorlab will complement the already diverse group of partner companies through their start-up perspectives. Their agility and innovation has permitted these start-ups to differentiate themselves in their respective fields. Please click below for more information.
We are looking forward to an exciting and fruitful collaboration.