In this collaboration (structured in two projects) we develop an automated tool to flag messages sent by planes which are suspicious of using weak encryption mechanisms. We mainly focus on detecting the use of classical ciphers like substitution and transposition ciphers. The tool flags messages and identifies the family of ciphers. We also aim to develop automated decryption techniques for the weakest ciphers.
On my path of moving lab’s code to more human friendly program, I usually write some CLIs, to ease configuration and deployment. When developing the client, I want to test it, and see how complex it is to use it. The best language to express that is a shell as it is probably how the (…)
To serve the 80 million forcibly-displaced people around the globe, direct cash assistance is gaining acceptance. ICRC’s beneficiaries often do not have, or do not want, the ATM cards or mobile wallets normally used to spend or withdraw cash digitally, because issuers would subject them to privacy-invasive identity verification and potential screening against sanctions and counterterrorism watchlists. On top of that, existing solutions increase the risk of data leaks or surveillance induced by the many third parties having access to the data generated in the transactions. The proposed research focuses on the identity, account, and wallet management challenges in the design of a humanitarian cryptocurrency or token intended to address the above problems. This project is funded by Science and Technology for Humanitarian Action Challenges (HAC).
Modulation recognition state-of-the-art architectures use deep learning models. These models are vulnerable to adversarial perturbations, which are imperceptible additive noise crafted to induce misclassification, posing serious questions in terms of safety, security, or performance guarantees at large. One of the best ways to make the model robust is to use adversarial learning, in which the model is fine-tuned with these adversarial perturbations. However, this method has several drawbacks. It is computationally costly, has convergence instabilities and it does not protect against multiple types of corruptions at the same time. The objective of this project is to develop improved and effective adversarial training solutions that tackle these drawbacks.
EPFL Campus Lecture with Marietje Schaake, President of CyberPeace Institute.

Many popular cloud applications collect enormous amounts of information on their users. […] Raising awareness of the issue, and providing ways to reduce it, is a worthy goal.

Encryption provides a solution to security risks, but its flipside is that it can hinder law enforcement investigations. A new technology called client-side scanning (CSS) would enable targeted information to be revealed through on-device analysis, without weakening encryption or providing decryption keys. However, an international group of experts, including EPFL, has now released a report raising the alert, arguing that CSS neither ensures crime prevention nor prevents unwarranted surveillance.
Point-of-Care Ultrasound (PoCUS) is a powerfully versatile and virtually consumable-free clinical tool for the diagnosis and management of a range of diseases. While the promise of this tool in resource-limited settings may seem obvious, it’s implementation is limited by inter-user bias, requiring specific training and standardisation.This makes PoCUS a good candidate for computer-aided interpretation support. Our study proposes the development of a PoCUS training program adapted to resource limited settings and the particular needs of the ICRC.
After 18 months of responding to the COVID-19 pandemic, there is still no agreement on the optimal combination of mitigation strategies. The efficacy and collateral damage of pandemic policies are dependent on constantly evolving viral epidemiology as well as the volatile distribution of socioeconomic and cultural factors. This study proposes a data-driven approach to quantify the efficacy of the type, duration, and stringency of COVID-19 mitigation policies in terms of transmission control and economic loss, personalised to individual countries.
P4 (Predictive, Preventive, Personalized and Participatory) medicine is called to revolutionize healthcare by providing better diagnoses and targeted preventive and therapeutic measures. In order to enable effective P4 medicine, DPPH defines an optimal balance between usability, scalability and data protection, and develops required computing tools. The target result of the project will be a platform composed of software packages that seamlessly enable clinical and genomic data sharing and exploitation across a federation of medical institutions across Switzerland. The platform is scalable, secure, responsible and privacy-conscious. It can seamlessly integrate widespread cohort exploration tools (e.g., i2b2 and TranSMART).
Recently, deep neural networks have been applied in many different domains due to their significant performance. However, it has been shown that these models are highly vulnerable to adversarial examples. Adversarial examples are slightly different from the original input but can mislead the target model to generate wrong outputs. Various methods have been proposed to craft these examples in image data. However, these methods are not readily applicable to Natural Language Processing (NLP). In this project, we aim to propose methods to generate adversarial examples for NLP models such as neural machine translation models in different languages. Moreover, through adversarial attacks, we mean to analyze the vulnerability and interpretability of these models.
Customer understanding is a ubiquitous and multifaceted business application whose mission lies in providing better experiences to customers by recognising their needs. A multitude of tasks, ranging from churn prediction to accepting upselling recommendations, fall under this umbrella. Common approaches model each task separately and neglect the common structure some tasks may share. The purpose of this project is to leverage multi-task learning to better understand the behaviour of customers by modeling similar tasks into a single model. This multi-objective approach utilises the information of all involved tasks to generate a common embedding that can be beneficial to all and provide insights into the connection between different user behaviours, i.e. tasks. The project will provide data-driven insights into customer needs leading to retention as well as revenue maximisation while providing a better user experience.
The overall goal of this project is to develop methods for monitoring, modeling, and modifying dietary habits and nutrition based on large-scale digital traces. We will leverage data from both EPFL and Microsoft, to shed light on dietary habits from different angles and at different scales.
Our agenda broadly decomposes into three sets of research questions: (1) Monitoring and modeling, (2) Quantifying and correcting biases and (3) Modifying dietary habits.
Applications of our work will include new methods for conducting population nutrition monitoring, recommending better-personalized eating practices, optimizing food offerings, and minimizing food waste.
The objective of the TMM project is to identify, at an early stage, the risks associated with new technologies and develop solutions to ward off such threats. It also aims to assess existing products and applications to pinpoint vulnerabilities. In that process, artificial intelligence and machine learning will play an important part. The main goal of this project is to automatically identify technology offerings of Swiss companies especially in the cyber security domain. This also includes identifying key stakeholders in these companies, possible patents, published scientific papers.
I’m quite a huge fan of functional programming, since I learnt about it some years ago. I was doing imperative programming for years and was quite used to it. But learning a new way to conceptualize programs was a real pleasure. Now that I’m deep into it, I want to apply it everywhere, even in (…)

Decentralized Ledger Technology has the potential to reshape the traditional financial system. An example is decentralized finance, which allows people to combine open-source building blocks into sophisticated financial products utilizing DLT. Central banks, as another example, face growing competition from private actors offering their own digital alternative to physical cash. However, the current lack of clear legal and technological standards prevents market players and institutions from fully exploiting the potential DLT.
This conference features latest research and insights on crypto-assets and asset tokenization, and their impact on banking and financial market infrastructures. The event combines a broad spectrum of stakeholders, which combine legal and regulatory, technological, financial and economic as well as civil society perspectives. It addresses academics and practitioners alike, and shall foster the public dialogue and interaction across institutions.
For more information about the event (speakers and agenda) please click below.
Today I Learnt (TIL): SASE [sæsɪ]- so what is it, how does it compare to a VPN, and should I use Tor? I heard about it from Ria at C4DT, who told me SASE is the new VPN.It might be better than VPN and will solve all the world’s problems. Well, first of all, what (…)
Digital privacy has become a top social concern for the expanding digital world. Societies are trying to define and navigate the future of digital privacy and determine technological solutions, new policies, and frameworks needed to protect individuals while maintaining support for digital services. There are several broad areas where the landscape is undefined, where policies still need to be developed, and where IEEE expertise may greatly impact the future of “privacy” on-line. The Digital Privacy Project is exploring how IEEE can best add to this discussion – bringing the perspective of technologists – to help advance solutions to protect personal and private information.
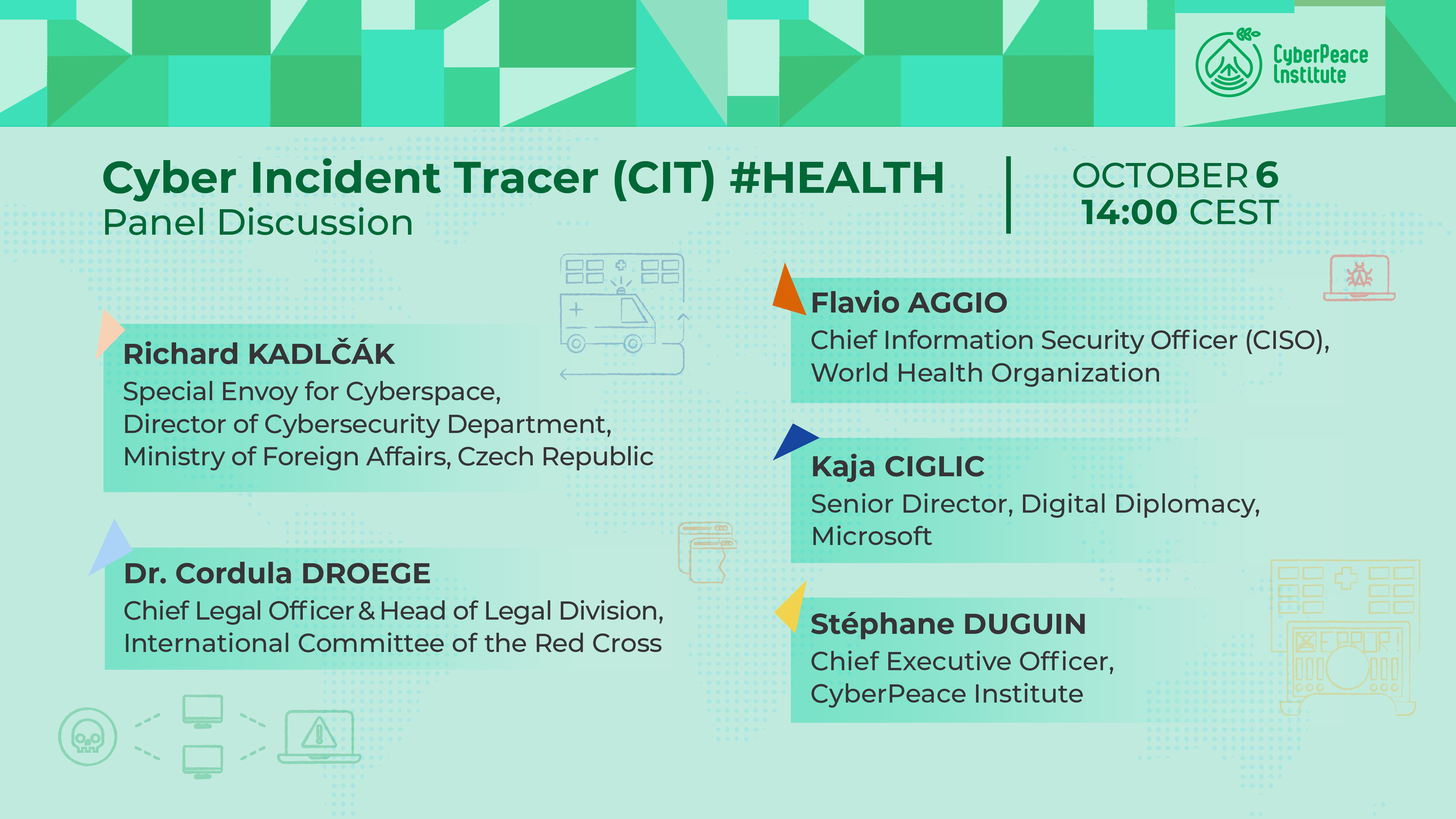
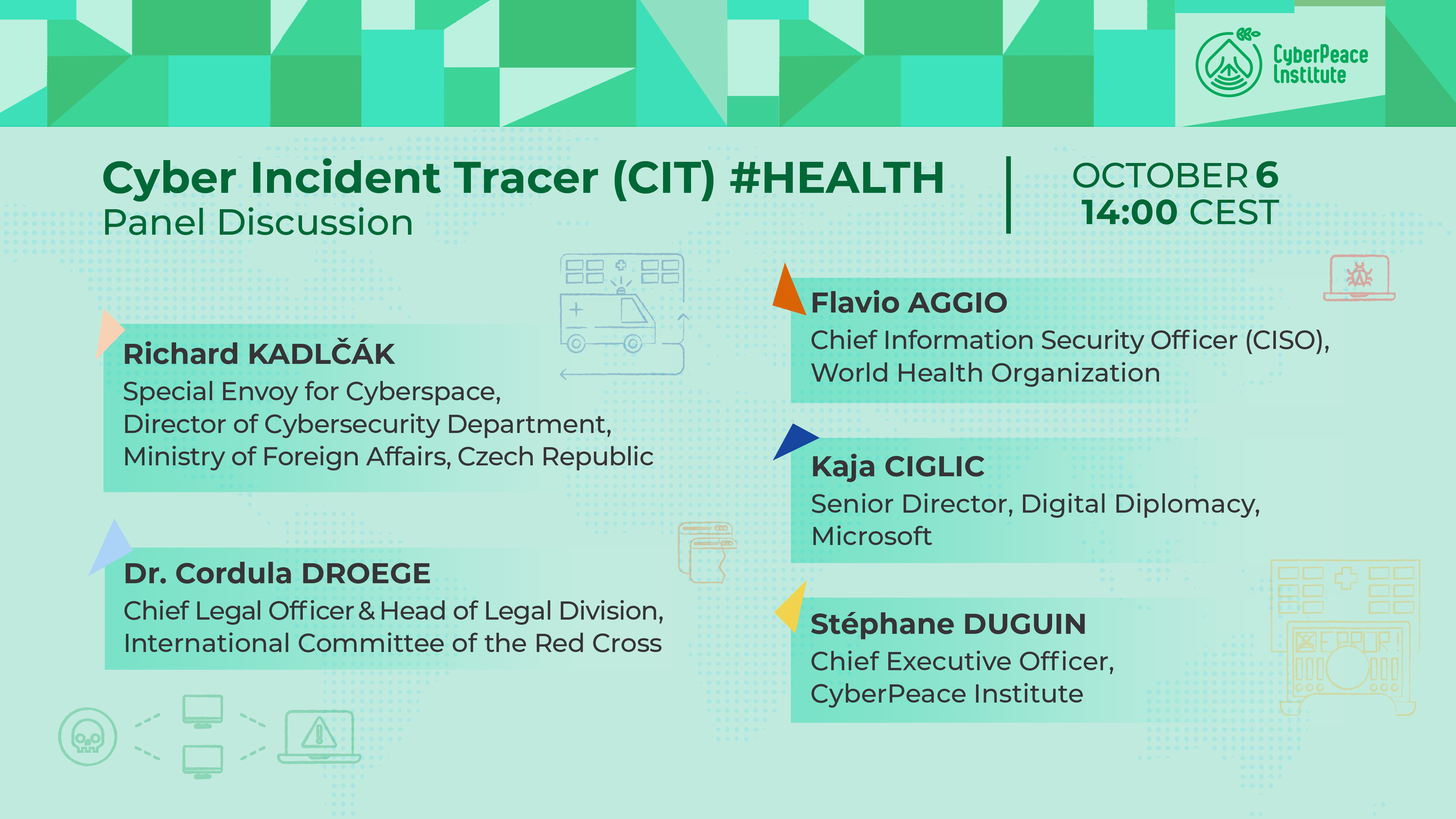
We will discuss how to bridge the gap in the availability of information relating to cyberattacks on the healthcare sector and how evidence-led accountability is an important contribution to reduce cyberattacks on this critical sector. Panelists will focus on how and whether understanding the scale and scope of attacks can improve decision making and operational and diplomatic initiatives to protect the healthcare sector.

At the C4DT Factory, one of our tasks is to develop demonstrators for research projects. The goal is to provide a quick introduction to a project, and allow visitors to interact and get a feel for the technology.
CLIs are very powerful, from the tip of fingers, you can quickly make the computer do anything you want. No need to wave your mouse around, hoping to find the right sub-sub-sub-menu where the feature you want is implemented. But it comes at a cost: for each command, you need to know how to write (…)

Concurrent programming is one the oldest and hardest issues in the Computer Science Book. For years, we have been using locks, big threads sharing the minimum, using optimistic reasoning for “how data will be updated”. And we are still stuck with the same issues of some part of the code “failing” to use the updated object, dead and soft locks with hard-to-see origins, and many many crashes.

The article Why Blockchain Is Not Yet Working goes over six points – for most of these points, research papers exist. For some of them test networks exist. Only one or two are solved in active main networks.

This conference will take place on October 15th, 9:00-17:00, at the Maison de la Paix of the Graduate Institute, Geneva (IHEID). It will address a number of key questions: How does a lack of digital trust manifest itself today? Is this justified, based on current privacy and security issues, or is it exaggerated? Understated? What lessons can be learned from other sectors on how to build the trust that will be needed for our digital future. What is possible in the digital future, and what will be lost without digital trust? And finally, how should that digital trust be built?
The event is jointly organised by IHEID’s Centre for Trade and Economic Integration (CTEI) and EPFL’s Center for Digital Trust (C4DT).
For more information click below.